Aryon Security Raises $29M to Shift Cloud Security from Detection to Prevention
Security teams have spent years being told their cloud visibility problem is the problem. Ron Arbel, CEO and co-founder of ...
Artificial Intelligence
Latest on TechSpective
TechSpective Podcast
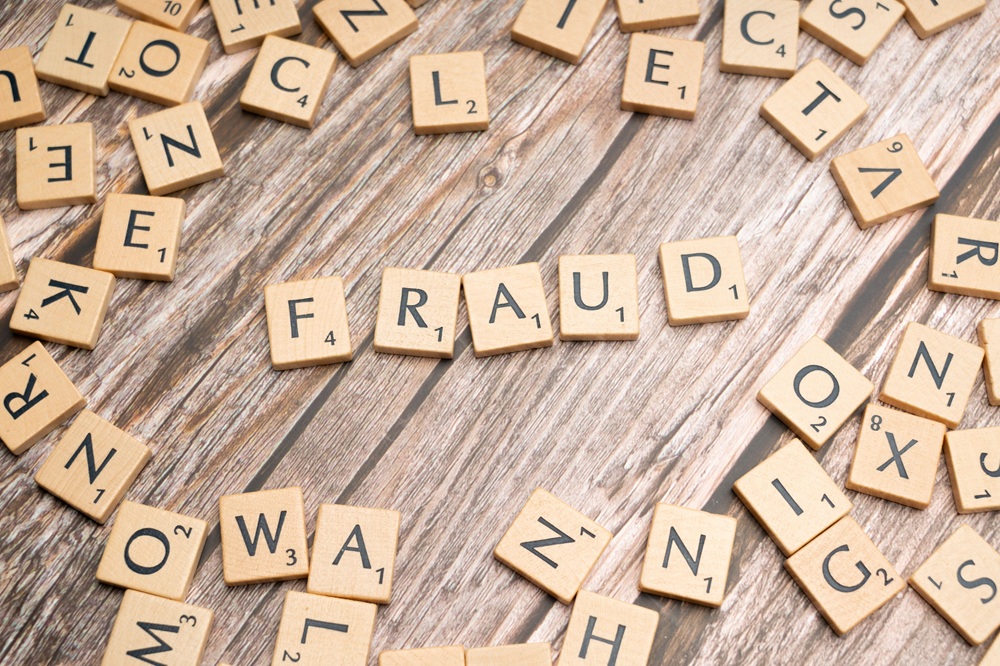
Remote Hiring Opened the Talent Pool — and the Fraud Surface
Before COVID forced everyone out of the office, hiring for most companies was a pretty localized exercise. You posted the ...
Tony Bradley
June 8, 2026
Analysis & Insight
CrowdStrike Turned an AI Wave Into Its Best Quarter Ever
CrowdStrike just posted its strongest Q1 in company history, and the company is crediting AI—not just as a product feature, ...
Tony Bradley
June 5, 2026
Artificial Intelligence
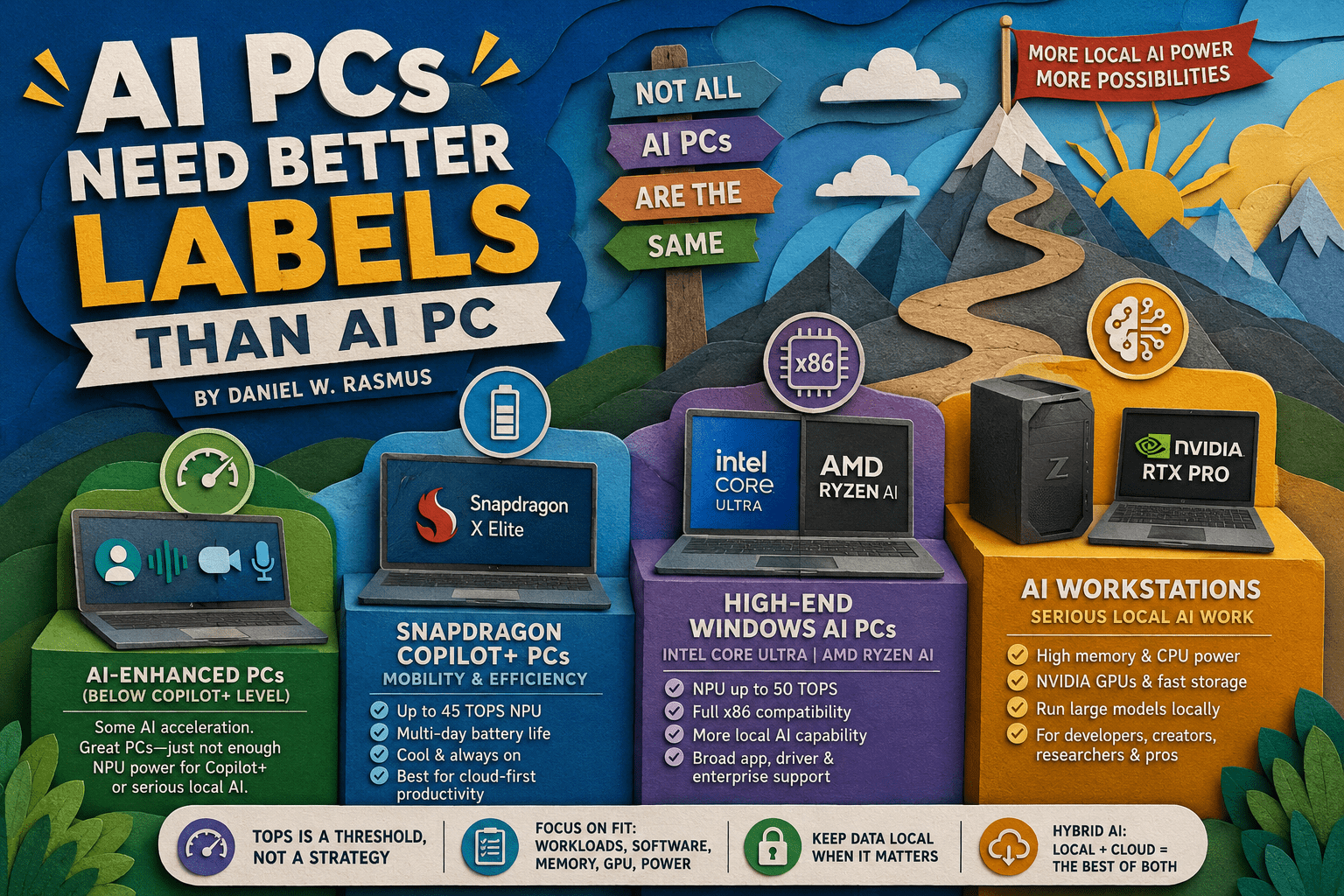
AI PCs Need Better Labels Than AI PC
The PC industry has never been shy about creating labels. Multimedia PC. Internet PC. Ultrabook. Creator laptop. Gaming rig. Workstation. ...
Daniel Rasmus
June 5, 2026
Emerging Tech
What Makes Quantum Computing So Different from Classical Systems?
For decades, classical computers have powered everything from simple calculators to complex global networks. They operate on a straightforward principle: ...
Harper Lane
June 4, 2026
Cybersecurity
Why Real-Time Fraud Prevention Is the Only Way to Stop AI-Driven Attacks
According to a 2025 PWC report, more than half of reported fraud now involves AI, including deepfakes, voice cloning, social ...
Evan Morris
June 4, 2026
Enterprise Technology
Cybersecurity
The OT Security Problem Nobody Wants to Own
Tony Bradley
June 3, 2026
There’s a paper mill somewhere with equipment that has been running for ...
The War on Deepfakes: How Google’s C2PA Integration at I/O 2026 is Fighting Back to Protect Our Reality
Rob Enderle
May 28, 2026
At this year’s Google I/O, the atmosphere at the Shoreline Amphitheatre was ...
N-able’s SOC Data Shows Half of Attacks Never Touch the Endpoint
Tony Bradley
May 14, 2026
A lot of organizations have built their security strategy around the endpoint ...