Part 8 of 16
All right, we’ve got some crazy guys, some crazy geeks—how can you trust them? Who can you really trust? Trust and security go hand in hand, right? It’s a binary condition. Right? Either you trust ‘em or not. Right?
You want to let him/her under the hood, give him/her root control to be able to make all those changes. It often takes a huge amount of faith in giving people the keys to the kingdom, so there’s a huge issue of trust that goes on there. Been arrested? Nope. Owe back child support? No. Background checks provide a piece of the data needed to vet a potential hire, but I find fault with this conventional approach – if that’s the only way trust is measured. It shows a complete lack of critical analogue thinking.
So, in response, I’m going to use the ugly and contentious phrase, “I like profiling.”
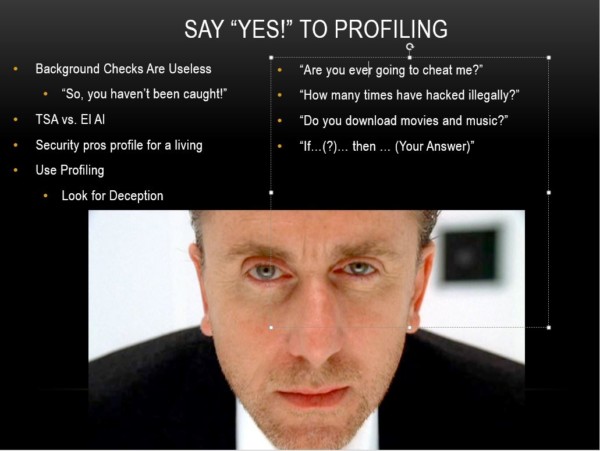
In cyber security, profiling is part of our jobs. That’s how we exclude 99.97 of the digital noise, ankle biting, and related IP crap, because we can profile – using technology. Yet, as soon as we talk about profiling humans, “Oh, that’s bad, that’s a bad thing.” We need to get over it.
We must find a way to let companies do some profiling before placing folks in mission critical positions with expansive root-control. Now, I’m definitely not saying or suggesting that I’m gonna profile, or that I care about, your sexual preferences, your religion or other personal beliefs that are not rooted in hate. (So I am clear… none of that stuff. I don’t care. That’s not what I’m talking about.)
I care about one thing, and one thing only during a profiling session. Are you being deceptive? Nothing else, nothing else ultimately matters because if you’re being deceptive, you’re trying to hide something that could potentially affect me, my organization, my infrastructure. I truly like the concept of industrial, psychological profiling where the vetting and profiling is based exclusively upon behavior and deception as it relates to the job… not one’s personal lifestyle.
For those of you who have traveled in Europe, the airport security process is different from what we go through here. In Europe they talk to you. They are trained to spot the tell-tale signs, (the tells) of deception. They know how to look for the micro-facial expressions and deception. In your interaction with security folks, deceptive characteristics are revealed in less than a minutes, without requiring you to take your clothes off or wearing a Speedo to get onto an airplane. (Just sayin’—sometimes it’s easier to wear a Speedo.) If you’re being deceptive, then you go to a more intensive interrogation.
Profiling—it works! And, we should embrace profiling when hiring folks for sensitive positions, in a non-invasive sensor-based manner, determine if they are being deceptive. I don’t care if it’s a Chinese or Iranian national, or anybody else. It doesn’t matter. Are you being deceptive is fundamentally the only thing I care about. The profilers know how to frame and phrase questions to match your trust requirements. Just don’t be so binary about it.
It’s about a $500 interview that uses industrial psychological profiling, a service available in major cities. It’s about rapidly identifying micro-muscular, retinal, and other auto-body reactions that put people under risk. It’s not about skin color, sexual preference or a belief in Little Green Men. (Depending upon where the LGM come from, of course … J )
“Under what conditions would you violate our company’s trust in you?” If someone answers ‘none’, they are being deceptive. We all have our breaking point. If your partner is threatened unless you hand over the latest technology details, what would you do? If you or the lives of your children are threatened, are you going to honor the confidentiality agreement you signed? What about if ‘they’ got a hold of those private photos on your computer?
The issue is to understand at what point do you reach the breaking point; the point at which you can no longer be trusted. It’s different for all of us. It’s not a simple yes/no binary choice. Like all things human, it’s a flexible dynamic. It’s another spectrum, an analogue spectrum, not an exercise in absolutism. Live conditions change second by second. Yet today’s hiring processes too often still employ broken methods.
Part 7: Autistics DO need to apply
Part 9: Binary trust is just an excuse to say ‘No’
Winn Schwartau is the CEO of The Security Awareness Company, the author of Information Warfare, Pearl Harbor Dot Com (Die Hard IV), and the upcoming Analogue Network Security.
- Hiring the unhireable: We can’t do it–It’s just too damn hard - September 10, 2015
- Hiring the unhireable: What to expect from the unhireable once you’ve hired them - September 8, 2015
- Hiring the unhireable: Perks for geeks - September 4, 2015