Part 9 of 16
Do you want all these hackers inside your company? I mean, working for your company. The bad guys are already in there – why add more, right?
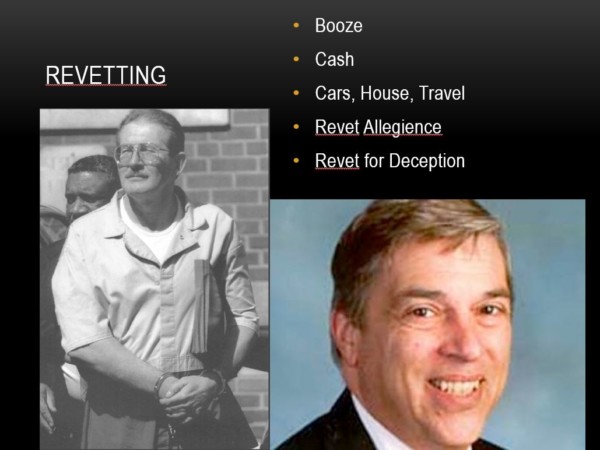
Why do we ignore the concept of periodic (analogue) revetting?
Just because you’re a good guy on day zero doesn’t mean you’re gonna be a good guy on day 180 or day 360. How much re-vetting did these two guys get—Aldrich Ames (CIA) and Robert Hanson (FBI)? Super senior counter-terror intelligence officials battling the Soviet Union, also working for the Soviet Union, yet neither received sufficient re-vetting. Re-vetting your mission critical people helps you find out what their stress is really like and what could cause them to go rogue, go bad or otherwise become an additional risk to your organization.
If you’re paying $100-200K per year for super talent with extraordinary access, shouldn’t you also be willing to invest .5% of that annually to protect your assets? It’s a measure of risk, paying a little attention to detail, and being willing to change a broken system. Start at your company.
We also need to start looking at government clearances. Clearances go back to this Cold War, binary mindset. “In order to work for us, you have to have a clearance.”
I was at DefCon and we were partying on the roof of the Rio. It was a gorgeous, beautiful night out, and a U.S. defense contractor was trying to do some recruiting. I introduced him to some folks, and, he was talking to this one guy, and he was like, “Oh, you’ve got the skills, you can do this, and everything sounds really good. So he asked, “Is there anything bad I need to know about?” The reply had a humorous spin. “Yeah, I’m Canadian.”
We need to rethink clearances and what do we mean by them because the clearances today and the structure we’re using is a relic of the Cold War. Inflexible, binary, and they deny us the flexibility that we need for the various types of network missions we have.
The sheer number of arbitrary discriminators that prevents governments from hiring the right people to defend nations astounds me.
Are all network operations and security jobs equal when it comes to the need for confidentiality and clearances? Absolutely not. Configuring a firewall is one thing. Analyzing big data is another. Active defense or designing the next Stuxnet understandably requires a higher level of trust (on the Trust Factor Scale, in my new book.)
Does a top secret clearance mean that you cannot have access to the tools that you need, that are perhaps even open source, because a government says, “That tool is secret”?
“Oh, I got it on the internet.” “Tough, it’s still secret.” It’s insane.
When I wrote Information Warfare in 1992, I had Feds come to my house wanting to know where I got access to all of that classified information. The mere thought that it was original thinking never occurred to them. But the best part was, every question they asked confirmed what I had written. The Feds (and subsequently Generals, etc.) were actually giving me top-secret information – and had no idea they were doing so.
We need to redefine the clearances or trust level required in the context of the job that needs to get done. One size does not fit all. We cannot hire foreigners to do huge amounts of the work that we need to get done to defend the country’s networks. We’ve got to rethink how we’re going to allow people in a closed society to really work together as part of a community
A friend of mine—brilliant, brilliant geek who only can work in the private sector because he owes the IRS $150,000, Feds won’t hire him because he’s quite clearly a security risk.
Is that right?
Another friend: his brother’s in jail for doing methamphetamine manufacturing. He can’t get a clearance because of what his brother did, but he has the skills. The Feds and our country suffer for lack of adapting to the 21st Century. We need to severely revisit what we mean and what we really need when we’re talking about clearances and what the day-to-day real objectives are. We need to find a way to make it happen.
Part 8: Let’s profile ’em all!
Part 10: Stop the drug testing
Winn Schwartau is the CEO of The Security Awareness Company, the author of Information Warfare, Pearl Harbor Dot Com (Die Hard IV), and the upcoming Analogue Network Security.
- Hiring the unhireable: We can’t do it–It’s just too damn hard - September 10, 2015
- Hiring the unhireable: What to expect from the unhireable once you’ve hired them - September 8, 2015
- Hiring the unhireable: Perks for geeks - September 4, 2015