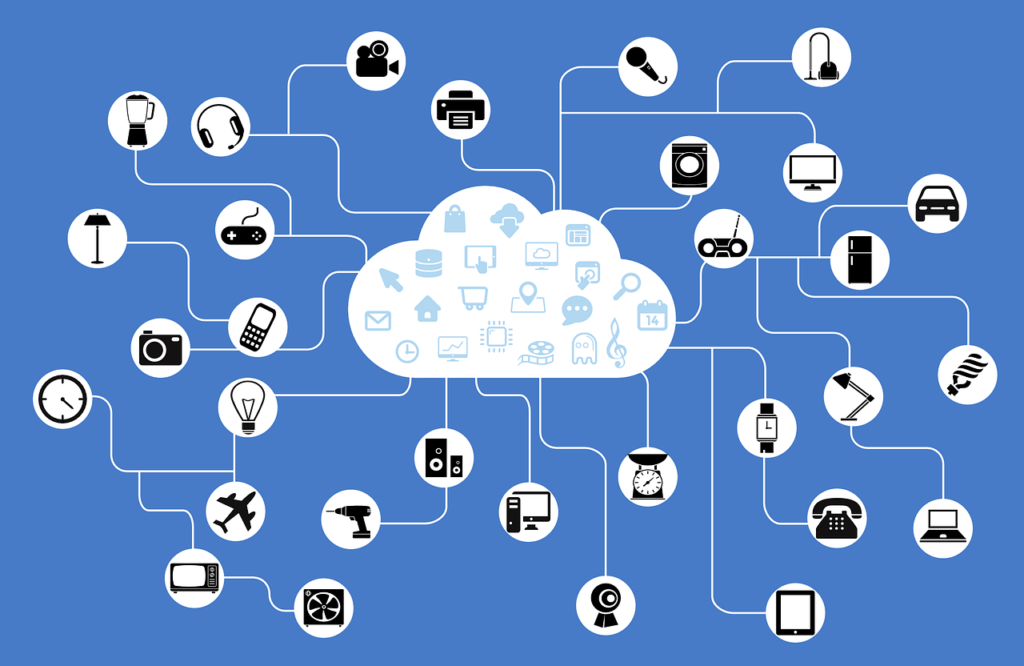
We are in the midst of an explosion of IoT-enabled devices and apps, connecting everything from the steps you take to the precise temperature of your room. Mundane inner-workings of office buildings are becoming fully automated and cars are now wirelessly coupled to the world around them. We are not just connected from the moment we wake up to the second we turn out the lights—processes that we put in place during our waking hours are carried out by devices overnight.
This connectivity might make things convenient, but it can expose its users to an unprecedented level of risk.
IoT is set to become a raging inferno of cyber-attacks and until recently, the entire ecosystem has largely been ignored. On an enterprise level, environments are now filled with hundreds of thousands of devices on constant alert, continually receiving information, exchanging commands, and dumping data. In October of 2016 we saw the first major use of compromised IoT devices to launch one of the biggest DDoS attacks in the history of the internet. March of 2017 brought with it a new variant of the attack which targeted and paralyzed a US college for 54 hours. The point here is that cyber-attacks are evolving at an alarming rate.
Is the answer to succumb to fear and downgrade progress? No, but we should be measured while we move forward into the world of the Internet of Things. You’ll hear people say things like “Do we really need our toaster to be connected to the internet?” Of course, it’s up to you to decide whether it should be—because you’ll likely have that option soon—but don’t let a facile argument distract from the power we could realize in IoT.
Technology has come too far not to capitalize on the possibilities it embodies. The constant exchange of information, the ease of device use, and the potential in limitless data analysis must continue for the betterment of all. Connected devices will become essential tools in an increasingly connected landscape.
The question then arises: just how do we do it?
The crippling DDoS attacks that paralyzed a school and took out Twitter, Spotify, PayPal, Verizon, Comcast, and others, were launched using a botnet built from IoT devices. The Mirai malware that made it all possible was estimated to have infected over 500,000 IoT connected devices. Hacks like these reveal that anyone is vulnerable to hacking, but they also show the sophisticated methods available to gain control of both the most mundane and advanced technology surrounding us today.
The benefits of IoT are clear—along with the obstacles and security demands. A true innovator chooses to move beyond those limitations and investigate what must come next to take advantage of a trend for the benefit of all.
Here are a few things for CIOs and CSOs to think about when considering the significant possibilities of IoT, the inherent risks, and the steps that need to be taken to protect against threats as they escalate.
- Privacy Concerns in an IoT World – Privacy is becoming a scare commodity when it comes to the advent of IoT. With our lives becoming increasingly digitally-based, we are our own worst enemy when it comes to private information. In order to ensure privacy, one must take increasingly difficult steps depending on the devices in scope. For instance, “always on” listening devices from top retail brands are a concern as they could potentially be compromised and used to eavesdrop on our conversations. Also, depending on the setup, the questions you ask the device are stored in local memory or in the cloud. The best protection comes in the form of device configuration. Many devices have physical mute buttons, the ability to wipe previous queries and encryption options. Fundamentally it is imperative to encrypt communications and data, and keep vital information accessible only to you.
- Secure Devices by Proxy – Should your devices have the ability to connect to the internet? If so, make sure that communication is proxied, logged, and whenever possible, examined by leveraging behavior analytics. The goal is to lock down devices before they join a botnet and the best way to do this short of securing the device itself is to create analysis choke points.
- Balance IoT Functionality with Data Safety and Set Limits – Businesses and consumers both require a level of understanding as to what devices are supposed to accomplish with the internet access they have been given. Logging, metrics and alerting need to come to the forefront of design when considering home or office networks. Should your Tide Dash button communicate with anything other than Amazon servers? Should your automatic light sensor really need to talk to anything other than when it is being asked to do something? The key here is to know the role of your device and sever its ability to communicate if it’s being abused by an attacker. We need to take more ownership of our connected “things.”
Despite the widespread concerns over IoT security, analysts predict that the technology is set to grow rapidly. Juniper Research predicts there will be 38 billion IoT connected devices by 2020. Connected devices will be adopted by consumers and organizations alike, posing a serious cybersecurity risk. This doesn’t mean we should silence our rapidly-connecting devices, putting them back in their tongue-tied infancy. Manufacturers, while currently not incentivized to secure devices, need to adopt security-first methodologies. IoT will continue to make our lives better, but in order to stem the tide of device abuse, we must put security first in everything we do.
Brad Bussie, Principal Security Strategist for Trace3, contributed to this article.
- IoT is Probably Your Biggest Enterprise Security Risk - August 12, 2017



Comments are closed.