There are many inconvenient truths regarding cybercrime. Every second in 2016, someone became a victim of cybercrime, meaning around a million people a day were affected. Cybercrime is a serious threat to businesses, individuals, and even nation-states. Three-quarters of Fortune 500 companies were targeted by hacks in 2016, alongside countless individuals. In a new report by Cybersecurity Ventures and Herjavac Group, the annual global cost of cybersecurity is predicted to reach $6 trillion by 2021, up from $3 trillion in 2015. This, of course, makes cybercrime big business. So, how has the issue of cybercrime reached a boiling point and what can be done to stop the already hot issue from heating ever closer towards meltdown? This article explores six seemingly disparate factors, that when combined provide a telling insight into the state of cybersecurity in 2017, and beyond.
1. Internet users
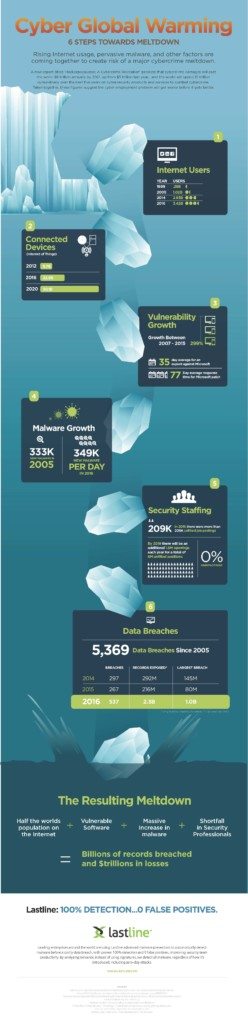
One obvious element to factor into the heightening levels of cybercrime is the increasing significance of the Internet. As more elements of business, pleasure and society become digitized and enter the cyber realm, the more Internet users will follow. This in turn creates a world of seemingly endless opportunity, in the form of billions of potential victims for cybercriminals. In 1999, 280 million people globally were Internet users. Moving forward to 2005 that number had risen to 1.02 billion, and in 2016 about half of the world’s population are using the Internet – a staggering 3.4 billion users worldwide.
2. Connected devices
The rise of connected devices now also plays a role in the diversification of opportunities available to cybercriminals. Where once people only engaged online on traditional devices – PCs, laptops, and later smartphones – in recent years the IoT phenomenon has facilitated a shift whereby the most commonplace of devices can store data, connect to WIFI, and ultimately become vulnerable to hackers. In a 2016 study over 85 percent of senior security professionals stated their belief that over 50 percent of IoT products could not be classed as secure. With high profile moves from leading companies such as Amazon into this field with their Alexa device, predictions are that we’ll see an increasing number of connected devices. In 2012 there were 8.7 billion connected devices, rising to 22.9 billion in 2016. This figure is projected to keep on rising, with estimates suggesting that by 2020 there will be more than 50 billion. Without adequate safety structures in place, this presents myriad opportunities for cybercriminals.
3. Vulnerability growth
Another area of exponential growth in the cybersecurity world is the amount of exploitable vulnerabilities. Between 2007 and 2015, the number of vulnerabilities grew by 299 percent. It takes on average 35 days to exploit a newly discovered Microsoft vulnerability, and 77 days to patch it. This is where the industry is lagging behind the criminals, as security strategies that are built on patching vulnerabilities and malware signatures are destined to fail.
4. Malware growth
The threat of malware has grown leaps and bounds in recent years, simply because the amount of new malware being created has exploded. In all of 2005, 333,000 new malware strains were discovered, but fast forwarding to 2016, reports show that 349,000 new malware strains are being discovered every day. 75 percent of the top 20 US banks were infected with malware in 2016, putting into perspective the potentially devastating consequences of not adequately dealing with malware.
Not only is the volume increasing, but so is the sophistication. New innovations in malware allow environment-aware code to avoid detection and lay in waiting for long periods of time, within the enterprise, until the attack sequence is optimal.
5. Security staffing
There are simply not enough people with the relevant skills to keep up with the increasing demand for security professionals. In 2015 there were over 200,000 unfilled job posts in the cybersecurity industry, and this number is expected to rise to 3.5 million openings by 2021. This chronic shortage of skills means that even if the problems discussed above are identified, organizations will be powerless to respond without the appropriate staff.
6. Data breaches
There have been 5,369 data breaches since 2005, but the increasing volume and severity of the breaches in recent years is a larger cause for concern. In 2015 there were 267 data breaches, but in 2016 that figure rose to 537, with over 2.3 billion records exposed. One billion of these came from a single hack on Yahoo! Bert Rankin, CMO at Lastline said of the breach at the time that ”with so many accounts potentially open for hacker use in distributing advanced malware, a data breach of this scale will no doubt have a far reaching impact on malware distribution worldwide.”
Where do we go from here?
These issues are pervasive, difficult to address, and largely out of the reach of most security professionals. There are some mitigating strategies – such as continuing to educate consumers, pressure IoT vendors to improve security, and recruit from outside traditional pools of candidates to fill open security positions – but relying on these alone will still leave enterprises largely open to attack.
In light of a rising tide of Internet users and connected devices, endless vulnerabilities from increasingly complex software, sophisticated malware that evades detection, and the extreme lack of qualified candidates, enterprises have little choice but to deploy technology solutions.
However, malware writers’ ability to iterate on variants renders signature or hash-based detection obsolete. Forward thinking enterprises are deploying advanced threat protection technologies that analyze behavior to detect advanced malware and anomalous network activity, and do so with greater efficiency and context that improves existing staff’s ability to keep up with the never-ending attacks.
As the risk of costly and damaging data breaches continues to rise towards meltdown, enterprises must use every tool available to them today to protect their networks, including advanced malware protection. The time to act is now.
- Cyber Global Warming: 6 Steps Toward Meltdown - September 1, 2017



Comments are closed.