Unless you’re living under a rock, you must be familiar with the massive ransomware attack called WannaCry that targeted more than 200,000 systems on its first day and spread worldwide very rapidly. In this article, I’ll share an in-depth analysis of this worldwide attack covering all aspects for you.
What is WannaCry Ransomware?
WannaCry Ransomware was a cyber attack outbreak that started on May 12 targeting machines running the Microsoft Windows operating systems. It affected companies and individuals in more than 150 countries, including government agencies and multiple large organizations globally. One such organization affected was National Health Services(NHS) in England and Renault-Nissan, which halted production in some areas as a result. The affected systems had all data encrypted and a message from the attacker demanding payment of a ransom within 3 days using bitcoins or else the cost would increase. Anyone who refused to pay would eventually lose access to their files and information stored in them.
How WannaCry Ransomware Spread and Infected the Windows OS
While initially, the experts thought the sudden spread was distributed by mass email spam campaign, the reality was quite different. The Malwarebytes Threat Intelligence Team discovered how it actually spread and wrote a detailed piece on the malware shared how the WannaCry Ransomware spread.
The NSA had discovered a vulnerability called EternalBlue in Windows systems but didn’t disclose it. After the massive attack, they were heavily condemned for it. However, Microsoft discovered this vulnerability in March and promptly issued a patch to fix it.
Most Windows users either didn’t take the update seriously or got lazy installing the necessary patch. As a result, the WannaCry Ransomware attack was able to exploit the SMB (Server Message Block) protocol on Windows machines that remained vulnerable.
What is EternalBlue?
EternalBlue is a leaked NSA exploit of the SMB protocol in Microsoft Windows that is used to propagate the malware in affected systems. EternalBlue leverages a technique called pool grooming—which is a type of heap spray attack on kernel memory structure. Targeting vulnerable Windows systems, it injects a shellcode that enables the attacker to use the IP address of the machine to directly communicate with the SMB protocol.
Further, without user interaction, it runs a script to check for a tool called DoublePulsar to verify if it is already installed and running on the system. DoublePulsar is a backdoor implant tool that was also developed by the NSA.
According to Malwarebytes Labs:
“The ability of this code to beacon out to other potential SMB targets allows for propagation of the malicious code to other vulnerable machines on connected networks. This is what made the WannaCry ransomware so dangerous. The ability to spread and self-propagate causes widespread infection without any user interaction.”
The DoublePulsar Malware infiltrated the vulnerable systems, enabling remote access and left the control of systems in the hands of the hacker who could then easily install any virus or malware, such as the WannaCry ransomware, on the systems.
Technical Analysis of WannaCry Ransomware and the Payload
As noted above, the hacker and creator of the WannaCry ransomware targeted vulnerable Windows PCs around the globe using the EternalBlue SMB exploit and DoublePulsar backdoor malware developed by the NSA to install WannaCry on the systems.
Eternal Blue – Piggybacking System
As mentioned above, EternalBlue is a piggybacking system and an SMB protocol exploit in Windows systems. This is how it all starts with EternalBlue exploit.
EternalBlue.exe runs a script on the target Windows computer executing the following commands:
- Send an SMB echo request to the target machine
- Setup the environment to exploit the vulnerable system
- Complete SMB protocol fingerprinting
- Attempt the exploit attack
- If successful, check for DoublePulsar malware
- Ping DoublePulsar for an SMB reply
DoublePulsar Malware
The DoublePulsar tool bypasses the authentication measures of a system and creates a backdoor to allow remote access. This means that without any user intervention, DoublePulsar successfully transfers the control of your system in the hands of the hacker.
DoublePulsar establishes a connection which allows the attacker to exfiltrate information or install any malicious code they choose—like WannaCry—on the exploited system.
Kill Switch Domain
One of the most interesting elements of the WannaCry ransomware attack is the highly-cited and publicized kill switch domain. This domain iuqerfsodp9ifjaposdfjhgosurijfaewrwergwea.com was included in the WannaCry script, and was designed to halt execution if it could connect with a hostname. However, since the domain was not registered, the attack continued to execute and spread.
As a personal opinion and analysis, I think the kill switch was kept in the code so that it could go undetected in high authority systems that maintain a sort of “sandbox environment” to trap the malware. In essence, it seems the inclusion of the kill switch was a mechanism to differentiate between a real and sandbox environment allow it to go unnoticed by cybersecurity tools and professionals.
Impact of WannaCry
The Wanancry ransomware infected millions of Windows systems in around 150 countries. The most affected countries were Russia, Ukraine, Taiwan and India. The worm also infiltrated many NHS systems across England halting their services as well. The Wikipedia entry for this attack contains more details on the affected organizations.
Once a system was compromised by WannaCry and the data was encrypted, victims were asked to pay a fee of $300 in the form of bitcoins in less than 3 days. After 3 days, the amount is doubled to $600. If the ransom was not paid within seven days, the attacker threatened to delete the files altogether.
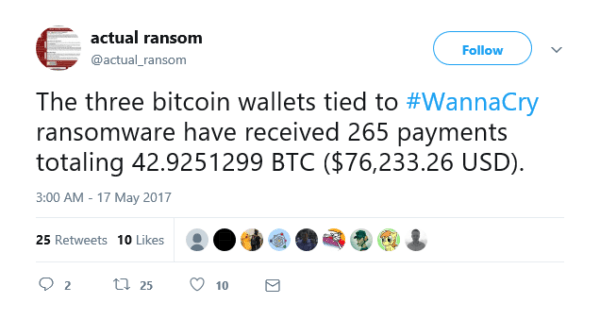
According to a tweet from @actual_ransom, the three Bitcoin wallets received around 256 transactions amounting to $76,233.26 USD. Not a bad income for a week or so of effort!
How was the WannaCry Ransomware Stopped?
Marcus Hutchins became an overnight hero when he accidentally saved the Internet from this malicious malware.
How did he stop it? As a cybersecurity researcher, Hutchins—who goes by @MalwareTechBlog on Twitter—was researching the WannaCry code when he discovered the kill switch in the script.
He discovered that before WannaCry infected a system or demanded the ransom to allow the owner to access the files, the script made a request to the domain name iuqerfsodp9ifjaposdfjhgosurijfaewrwergwea.com.
Marcus discovered the domain was unregistered. So, he went ahead and registered the domain name for $10.69 at NameCheap.com and pointed it to a sinkhole server he was hosting in Los Angeles to get more information about the malware.
Suddenly, the rapidly spreading WannaCry ransomware attacks dropped off and this accidental save made Marcus Hutchins a Hero who saved the Internet from an impending doom.
FYI: The 23 year old Marcus Hutchins was later arrested while attending the Def Con security conference in Las Vegas. Authorities have pressed charges alleging that Hutchins is responsible for developing malware designed to capture the online banking sessions of users. Working under the pseudonym “Kronos”, Hutchins is said to have developed and maintained this code to sell as kits for online cybercrimes.
Summing Up the WannaCry Ransomware Attack
The main thing that was reinforced by the speed and success of the WannaCry ransomware attack is the importance of keeping systems patched and up to date. If you’re using outdated, vulnerable software, it is time to either update it or replace it entirely.
You should also uninstall or disable unnecessary services and protocols. Malware attacks often exploit these services and protocols as an attack vector.
The most important less when it comes to ransomware is to back up your data. Always ensure you have a recent / current backup of your files on a remote system or housed in cloud-based storage. You should never be forced to pay the ransom or risk losing your data. Even if your system is compromised by ransomware, you can just restore your backed up data and resume normal operations.
- WannaCry Ransomware: A DetailedAnalysis of the Attack - September 26, 2017



Comments are closed.