Data is essentially the “oil” or “gold” of the Internet Era. Data is crucial for both businesses and individuals—and has significant value for cybercriminals. Data needs to be protected, but that is often easier said than done. Encryption is one of the most effective and widely used methods for protecting data, but the security it provides is a function of the strength of the algorithm, and you need to have a balance between security and performance—a balance that will be even more difficult as quantum computing continues to evolve. Intel recognizes the challenges that come with encryption and is working to enable the future of computing by accelerating encryption at the hardware level.
Encrypt Everything
It is commonly accepted that sensitive or important data is encrypted to protect it from unauthorized access. One of the pervasive challenges of data protection, though, is who decides what is sensitive or important? And—perhaps more vitally—what is the process for continuously making that determination and actively ensuring that data is appropriately tagged and protected?
Systems that rely on data classification almost always fail to achieve the desired goal. Someone has to be responsible for assigning the classification. If that is a central team or individual, the sheer volume of data that needs to be assessed and classified can quickly become overwhelming—leading to either significant delays, errors in classification, or both. Some organizations rely on the individual who creates the data to assign the classification, but that also often leads to errors. The net result is a system that puts a significant burden on users, and provides a false sense of security, but generally fails to adequately protect data.
One alternative would be to encrypt everything. Remove the need to determine the value or classification of the data, and simply protect all of it. That comes with some challenges as well, though. Encrypting data—especially when using stronger, more complex algorithms—is computationally intensive. It requires a lot of processing power, and the process of encrypting and decrypting data introduces latency and impacts overall performance.
The ultimate goal is to be able to seamlessly encrypt everything and protect all of the data, but with minimal impact to the processing capacity or performance of the system. That is where Intel’s efforts with Crypto Acceleration come in.
Crypto Acceleration
Intel is focused on reducing the cost of the cryptographic algorithm computations used to encrypt data. With its role as a primary provider of processors and chip hardware, Intel is on the frontline of innovations and is uniquely positioned to be able to improve encryption at the hardware level.
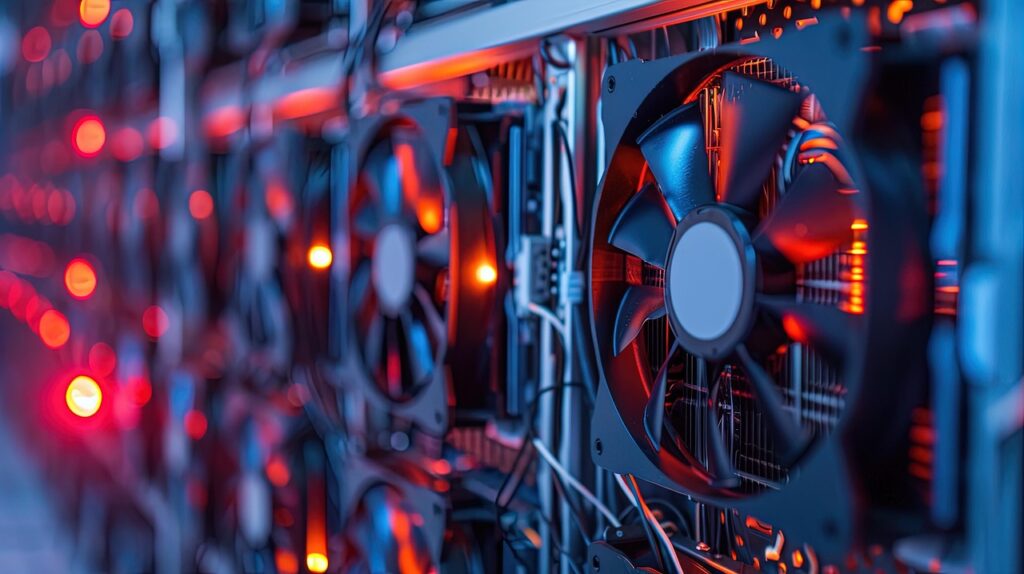
Wajdi Feghali, Intel Fellow in the Intel Security, Architecture and Engineering Group, explained that the Intel’s new 3rd generation Intel Xeon Scalable processers, code-named “Ice Lake,” brings several new instructions coupled with algorithmic and software innovations. The net result is that Intel Ice Lake processors deliver cryptographic acceleration and deliver breakthrough performance for the most widely used cryptographic ciphers.
Intel focused on improving performance for the most widely used TLS (transport layer security) ciphers. A blog post about the crypto acceleration effort explains, “Starting with the instruction set architecture (ISA), Intel introduced several enhancements designed to significantly increase cryptographic performance.”
The Xeon Ice Lake processors include the following enhancements and capabilities to improve cryptographic performance:
Public-Key Cryptography
New support for “big number” multiplication. Combined with software optimization techniques, such as multi-buffer processing, the new ISA instructions provide significant performance improvements for RSA and elliptic curve cryptography.
Symmetric Encryption
Instruction enhancements increase performance for AES symmetric encryption, and related algorithms. The new instructions support vector processing of up to four AES blocks simultaneously, providing a performance benefit to all AES modes of encryption.
Hashing
Intel Ice Lake processors also boost performance for SHA (secure hash algorithm) encryption with Intel SHA Extensions. The new instructions provide a significant performance improvement for SHA-256 encryption.
Function Stitching
Intel pioneered the technique of function stitching—taking two encryption algorithms that typically run sequentially and “stitching” them together into a single, optimized algorithm to maximize processor resources and performance.
Multi-Buffer
Intel developed a capability to process multiple buffers simultaneously. It is an efficient technique that enables processing of multiple independent data buffers in parallel for cryptographic algorithms—resulting in significant performance improvements.
Future of Computing
The more technology evolves, the more everything is data. It’s crucial to encrypt the data that needs to be protected, but cumbersome to try and figure out and maintain which data that is. The obvious solution for the future of computing is to simply encrypt everything but doing so will require innovations like Intel has developed to enhance and accelerate cryptographic functions so that data can be encrypted and protected without affecting performance.
- Navigating Cybersecurity Complexity - July 18, 2025
- AI Voice Clones and Mobile Phishing: The Cyber Threats You’re Not Ready For - July 11, 2025
- Rethinking Cloud Security for the Evolving Threat Landscape - July 11, 2025