While mobile threats are new to the game in comparison to desktop malware, the targets are becoming more predominant in the everyday life of users. With the number of mobile devices increasing, it is no wonder that thieves are working to develop new ways to deliver malware to the devices. In this case, we are looking at the threat known as drive by downloads.
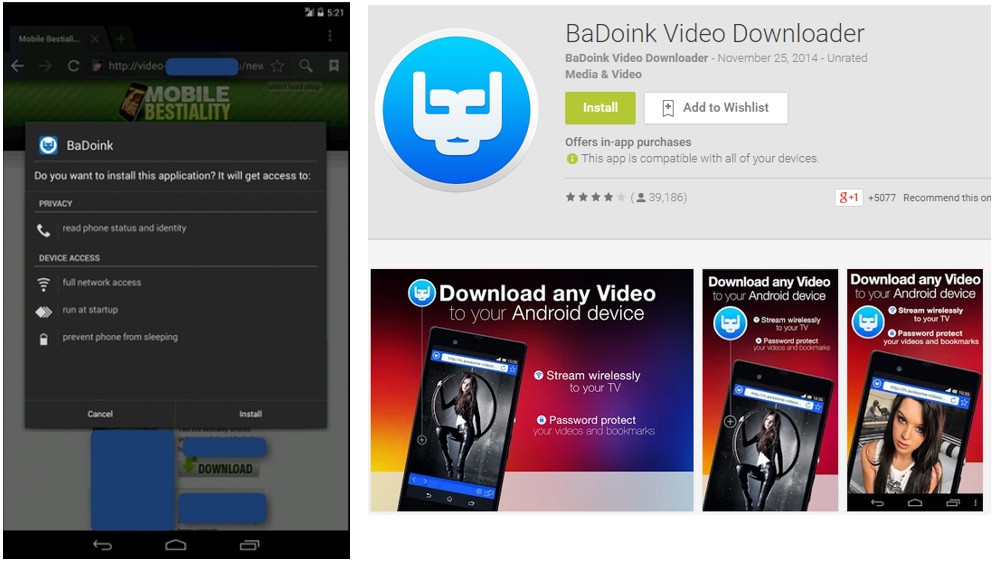
On the left is what a user will see once they browse to consume adult entertainment in a less than savory environment. This pop up is offering a “better way to view the content” by downloading their app. However, this is a direct download. This raises suspicion, because if there is an actual legitimate app, then you would just download it from the official play store or be taken there by the pop up. Directing users to the play store is not an uncommon practice for websites to provide an app for a better mobile experience. You often see this with forums or news sites.
When a website requires a direct download and installation of a third-party app, it should be scrutinized heavily. On the right we see the official legitimate download for Badoink on the Play store. Simply linking a user to this would be a much easier thing to do than asking a user to side load a third-party app.
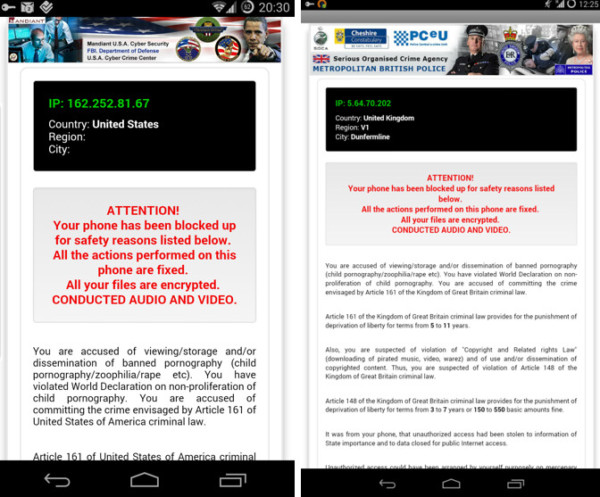
If the user has managed to side load the app, despite all warnings from the Android OS NOT to do this, they will see the app is now installed just like any other. Upon running the app their phone will become locked with the familiar looking FBI ransom. This Ransom accuses the user of browsing BANNED pornography and demands payment of $300 in moneypak/BitCoin.
Although it is implied through the ransom message that your files are encrypted, it does not have permission to do any such thing – at least in this strain we analyzed. Rebooting the phone will also produce the same effect, because the user gave the app permission to do this on install. At this point the only way to remove the app would be to reboot the device in safe mode and uninstall it from there. Safe mode will prevent anything but the necessary system apps from running – just like windows. Getting there can vary, but any device since the likes of the Nexus One should be able to boot to it. The only way malware could foreseeably get around this, was if the device was rooted, the malware looked for this, and then exploited this to install itself to also run in safe mode.
Ensuring that safe browsing practices are followed along with an understanding of safe areas to download apps, all while having a security layer of a strong, proven mobile AV installed, will help to keep users safe from these drive by tactics. While the malware is designed to trick users, just like phishing, it often does not take much to see beyond the potential scam in how these methods are displayed to users.
Part 1: Today’s mobile threat landscape
Part 3: Mobile threats: Google Play – Malware from the store
- Mobile threats: Remote access Trojans (RATs) - July 7, 2015
- Mobile threats: Premium SMS malware - July 6, 2015
- Mobile threats: Google Play – Malware from the store - July 3, 2015