Threat actors are always looking for new ways to infect as many users as possible with their malicious payloads. As a means to this end, these threat actors get creative with the types of files they use to deliver their attacks. This is an attempt to get past the early phase of threat detection, which is based on checking file types before allowing the file to be delivered.
[the_ad id=”4603″]Our threat detection center recently detected a large-scale malware campaign using that style of evasion. Malicious Windows Shortcut files (also called LNK files due to their file extension) in nested ZIP archives numbering in the thousands were observed hitting our Advanced Threat Detection system. This campaign lasted for a full week before slowing to a small but steady trickle.
The shortcut file itself runs PowerShell with privilege escalation and a provided script embedded in the shortcut. The privilege escalation does offer some form of protection for some more cautious users as most newer versions of Windows require that a user allow PowerShell to be run with administrative privileges. However, this also may allow the file to evade some sandboxes as well since it requires user interaction to actually download the payloads.

The script itself contains a list of hacked sites that it attempts to download and run two executable files from. Using a list of sites helps to ensure that if one site is taken down, others may still be reachable to download the payload. In an attempt to evade some network-level detection, the files are declared as PNG image files by the server then renamed to executables on the victim’s computer. Although the exact files downloaded seem to vary a bit, the threat type of the two files seems to remain the same. The first file is Locky (Osiris variant) and the second is a Trojan Horse.
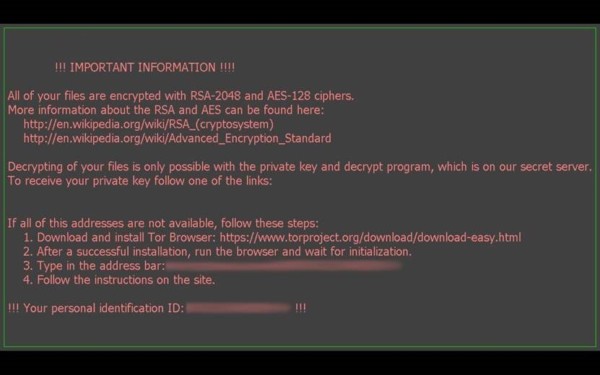
Locky is a relatively new ransomware and the Osiris variant observed is the latest incarnation of it, first being observed December 2016. Unlike some earlier ransomware, there is no known way to decrypt files that have been encrypted by Locky. This leaves restoring the files from backup (if one is fortunate enough to have the files backed up) or actually paying the ransom—not a generally encouraged practice—as the only possible ways of recovering the files.
The Trojan is much less straightforward and we were unable to identify its specific family. It makes numerous modifications to the registry that vary depending on the version of Windows running on the PC. Interestingly, on Windows XP it downloads and installs a specific but valid Windows Update file, most likely to ensure that PowerShell 2 is installed on the system for malicious code to be run later in the execution. Numerous network requests were made that seemed to fail, so it’s likely that the full intended execution was not observed. It’s possible that it was trying to download more payloads, exfiltrate sensitive data, or join a botnet.
As the market for ransomware and other malicious threats continues to grow, the number of novel techniques to evade detection will continue to grow with it. Protecting oneself or their company is crucial but multi-faceted. Advanced threat detection and next generation malware detection is critical, but much more is needed for full data and asset protection:
· Proper and regular backups of critical data can prevent the need to pay a ransom or recreate data
· Firewalls capable of protecting modern, intelligent perimeters, can protect against intrusions and help identify existing infections that try to communicate with external servers
· User training on suspicious emails, links, and web ads will help strengthen your last line of defense.
Security is not about a single solution, but multiple layers of different types of protection, ranging from email security gateways to user training on how to recognize spam. By deploying only part of this ecosystem, you leave your network open to attackers who are laser-focused on making you a victim.
- Don’t Be Fooled by File Types - February 21, 2017



