The responsibilities of IT managers are seemingly endless.
Not only do they have to stay top of security patches and software updates, but they also need to oversee the expenditures that surface from the IT team—making sure that the IT department’s budget is used cost-effectively.
All of this, while the IT managers also have to coordinate with HR for hiring the right IT consultant and educating the end-users on new software or tools that have been onboarded.
Sigh…
With all the tasks involved in managing an entire IT ecosystem, companies are bound to have a “chink” in their proverbial IT armor.
Sadly, cybersecurity is that one thing that’s often left overlooked.
Most companies don’t take cybersecurity seriously enough—not until something catastrophic has already happened.
If you’re one of the few competent IT managers who is looking to establish and fortify their IT defenses despite how busy they are, then you’re in the right place.
Allow me to share with you several cybersecurity tips that you can implement as a manager despite your busy schedule.
1. Manage everything in one platform
If you want to have a bird’s-eye view of your IT ecosystem to make sure that everything is in tip-top shape, then you need to manage everything in one platform.
A tried and tested IT management tool like Cloud Management Suite (CMS) is one of the best platforms you can use to that end.
Because CMS shows your entire IT operation and the health of your devices in one place, you can monitor your devices better.
You can tell which among your devices are vulnerable against cyber attacks and which ones are safe.
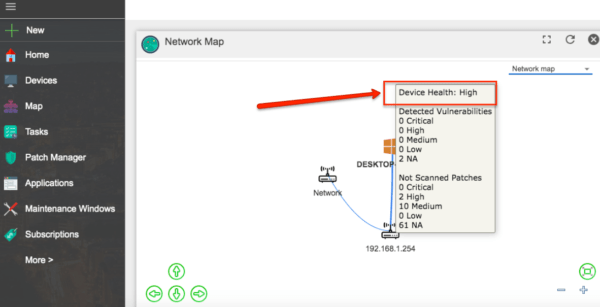
You can also use the platform to respond to security alerts in real-time since CMS allows security managers to detect running applications and kill processes instantly — regardless of the devices’ location and status.
What’s more, you can even deploy security patches through the platform automatically, making it easier for IT managers to ensure that the devices on their networks are up to date and secure.
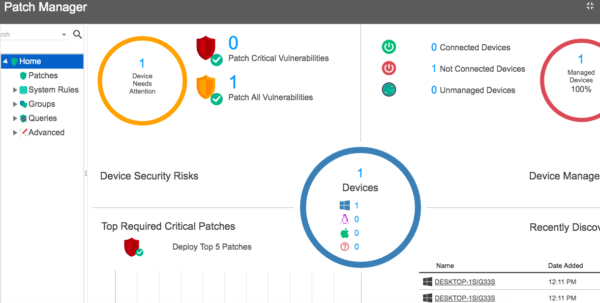
These are just some of the many ways CMS can help IT managers with securing their IT operations against cyber attacks in the easiest and simplest way.
Here are several other features that IT managers would be delighted to know about CMS:
- Software distribution
- Remote desktop access
- Inventory history
- Compliance reports
- Etc.
It’s also worth pointing out that CMS is a cloud-based tool. That being said, you can access the platform through the internet using a web browser.
2. Document your cybersecurity workflows
Every time your company hires a new IT consultant, you have to educate them about the culture and workflow that your company follows.
Doing so can involve quite a lot of manpower hours to train and align others.
Not only will the new guy’s time be spent on learning and training, but the person conducting the training also suffers.
What, then, is the solution to this challenge?
Document your processes.
You can do this via recorded webinars, screencasts, or just through Google docs—the important thing is you document your process.
For starters, you can even create a Trello board for the purpose of streamlining your process. You can then create a Trello Card for each job title where you’ll attach the nitty gritty of their responsibilities, roles, etc.
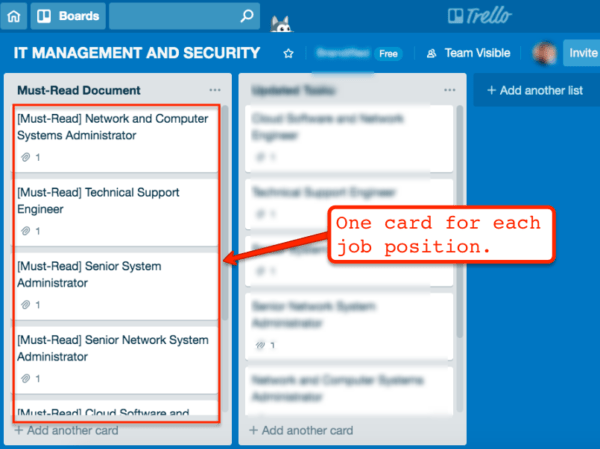
When you start documenting your cybersecurity workflows, you’d only need to direct your new team members to the document so they can study it by themselves.
This helps you avoid having to teach your new hires (or transferees from other departments) from the ground up.
Just by watching or reading through the documentation of how your cybersecurity system works, you can keep your new team members up to speed the quickest way possible.
3. Schedule regular team meetings and training
The adage “prevention is better than cure” rings true in the realm of IT management.
After all, depending on the kind of cyberattack your company experiences, you can easily face thousands (if not millions) of dollars’ worth of impact and damages—something that some companies can’t come back from.
While there are certainly tools like CMS that can help keep your company from falling prey to a good number of cyber attacks, you need to train and educate your team regularly about the things they can do on their end to protect the company against cyber attacks.
The good news is, with the help of online tools like ezTalks, you can set up internal training sessions in a matter of minutes.
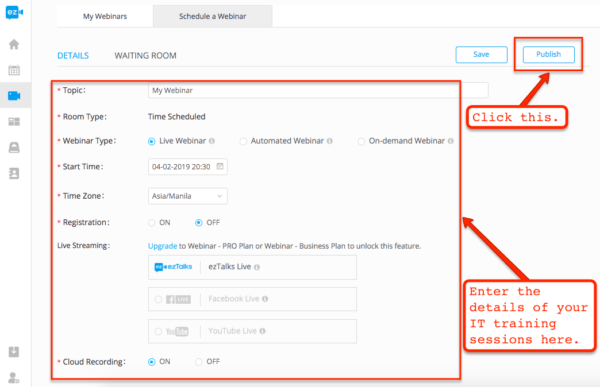
After you click the “Publish” button, you can start inviting people to your webinars.

It’s that easy.
Now that you can gather your team in a single place, you can start training them. These are some of the many things you can cover in your pieces of training:
- Basics of cybersecurity
- What makes their devices vulnerable to attacks
- Common patterns of hackers
- Common IT mistakes that compromise the network,
- Etc.
Remember, the more educated your team is about the workings of hackers and nitty-gritty of how cyber attacks are often run, the less likely your company will fall prey to cybercriminals.
With all the tasks you have on your plate as a busy IT manager, the last thing you want to happen is to become even busier due to your company’s network getting compromised.
Invest in training your team.
The learnings and sharpening they’ll get out of your regular training sessions will keep them from making unnecessary mistakes in the future, therefore, helping you avoid needless—let alone, time-consuming—firefighting tasks.
What’s next?
If you’ve been an IT manager for quite some time now, then chances are, you’re not a stranger to how crazy busy things can be when managing an entire IT ecosystem. Please share your ideas and your tips for what has worked for you in the comments section below.




Comments are closed.