For over a decade, HP Inc. has operated under a philosophy that sets it apart from the majority of the PC and print hardware market: security cannot be an add-on software layer; it must be intrinsic to the hardware itself. While many competitors were satisfied bundling third-party antivirus trials with their laptops, HP was busy architecting the Endpoint Security Controller (ESC), a physically isolated chip that acts as a “root of trust.”

This foresight has allowed HP to stay years ahead of the curve, particularly regarding future-proofing. A prime example is HP’s proactive stance on Quantum Computing threats. Long before quantum computers could practically break current encryption standards, HP began integrating quantum-resistant cryptography into its firmware. This level of preparation—anticipating a threat horizon that is years away—defines HP’s culture. It explains why its latest Wolf Security report, “Malware in Motion,” is not just a list of problems, but a validation of its hardware-enforced isolation strategy.
The 2025 Threat Landscape: Deception in Motion
The Q3 2025 HP Wolf Security Threat Insights Report paints a disturbing picture of the modern cyber battlefield. The era of the “obvious” virus is over. We have entered the age of “Malware in Motion.”
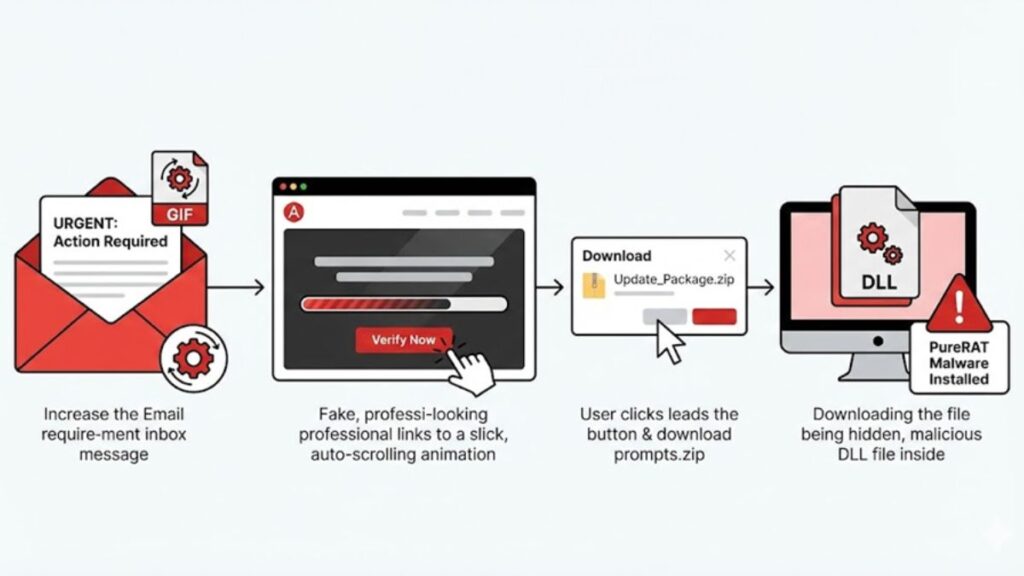
According to the report, threat actors have moved beyond static phishing emails to highly sophisticated, animated user experience (UX) manipulations. Attackers are now using polished, professional-grade animations to mimic legitimate processes.
For instance, the report highlights a campaign impersonating the Colombian Prosecutor’s Office. It didn’t just send a link; it directed users to a fake government site featuring slick auto-scroll animations that guided targets to a “one-time password.” This visual legitimacy lowers the user’s psychological defenses, tricking them into downloading a password-protected archive that installs PureRAT malware.
Similarly, fake Adobe updates now feature staged animations of installation progress bars. The user thinks they are watching a legitimate update; in reality, they are installing a modified version of ScreenConnect, a remote access tool that hands the keys of the kingdom to the attacker.
The Commoditization of Cybercrime
What should terrify business buyers is not just the sophistication of these attacks, but the ease with which they are executed. The report details how hackers are utilizing “Malware-as-a-Service.” Tools like Phantom Stealer are available for purchase on hacking marketplaces, complete with subscription models and regular updates.
This lowers the barrier to entry significantly. A threat actor no longer needs to be a master coder; they just need a motive and a crypto wallet. Furthermore, these attackers are abusing trusted platforms like Discord to host their payloads, bypassing domain reputation filters. By the time a traditional security scanner realizes that the traffic from Discord is malicious, the payload—often hiding in a DLL sideloading attack—is already executing.
The PC and Printer Convergence
While the “Malware in Motion” report focuses heavily on PC endpoints, the implications for the printer landscape are equally dire. In the modern hybrid office, the printer is a sophisticated IoT endpoint with its own BIOS, firmware, and network connection.
If attackers are using such sophisticated methods to breach PCs, unmonitored printers become the path of least resistance. HP has long recognized this, extending Wolf Security to its print fleet. The same principles—Memory Shield, run-time intrusion detection, and self-healing BIOS—apply. For a business buyer, purchasing a fleet of PCs and printers that do not talk to the same security stack is leaving a massive gap in the defensive perimeter. If your PC blocks the DLL sideloading attack but your printer allows a lateral movement intrusion, the network is compromised.
Architecting Defense: Isolation Over Detection
HP uses the data from these reports to refine a strategy that is fundamentally different from its peers: Isolation.
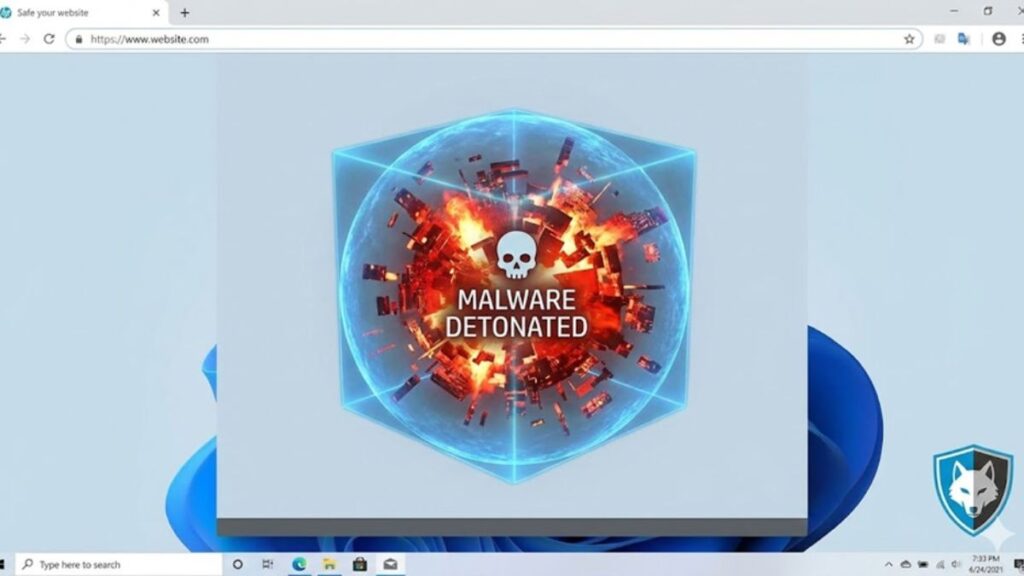
Traditional antivirus (AV) and Endpoint Detection and Response (EDR) rely on detection—they have to recognize a file as bad to stop it. As the report notes, highly evasive samples like the PureRAT campaign were only detected by 4% of AV tools on average. Relying on detection is a losing game.
HP’s response, via HP Wolf Security, is to assume everything is malicious. By using micro-virtualization, HP isolates risky tasks—like opening that fake Adobe PDF or clicking that Discord link—inside a virtual container. If the file is malicious, it detonates inside the container. The user closes the window, and the threat is gone. It never touches the host operating system.
The report validates this approach with a staggering statistic: To date, HP Wolf Security customers have clicked on over 55 billion email attachments, web pages, and files with zero reported breaches. That is not a margin of error; that is a paradigm shift.
Why HP Leads the Pack
Business buyers must look at the “Malware in Motion” report as a warning: software-only defenses are failing. Attackers are modifying legitimate tools (like ScreenConnect) and patching Windows 11 memory integrity defenses before deploying their payloads.
HP leads its peers because it controls the hardware. When malware attempts to bypass OS protections, HP’s hardware-enforced security acts as a backstop that the malware cannot see or touch. Competitors who rely solely on the operating system vendor or third-party software agents are vulnerable to the exact evasion techniques described in this report.
For the business buyer, the choice is clear. You can buy a device and hope your employees never fall for a convincing animation, or you can buy a device that renders the mistake irrelevant.
Wrapping Up
The Q3 2025 Threat Insights Report serves as a stark reminder that cybercriminals are innovating just as fast as the tech industry. With animated lures, trusted platform abuse, and subscription-based malware, the “human element” remains the biggest vulnerability. HP’s continued dominance in this space stems from its refusal to rely on the user making the right choice. By leveraging hardware-enforced isolation and quantum-resistant architecture, HP ensures that even when a user is tricked by a slick animation, the business remains secure. In a landscape where detection rates are dropping, HP’s architecture of isolation offers the only guarantee that matters: resilience.
- The Coming AI Storm and Why AMD’s coming July Event Is the New Industry North Star - May 5, 2026
- Intel’s 18A Redemption and Why the Analysts Are Finally Catching Up to the AI PC Reality and What Grove Would Do to Finish the Fight - April 24, 2026
- The Great Disconnection: Why Gen Z is Ditching Cellular for Satellite Safety and the Rise of the O-Boy Era - April 22, 2026