As the stress of tax season approaches so are the hopes of cyber criminals looking to take advantage of unsuspecting consumers. Cyber criminals are looking for:
1. People submitting taxes online
2. People waiting to do last minute returns, to intercept most or all of your information.
Both scenarios continue to make tax season one of the most profitable time of the year for spammers and hackers alike and it’s showing no signs of stopping anytime soon. Unfortunately, unlike holidays, taxes are unavoidable. As we continue to monitor our threat intelligence networks at Barracuda Central we see targets extend much further than the United States to defraud not just individuals but ultimately the government(s) as well.
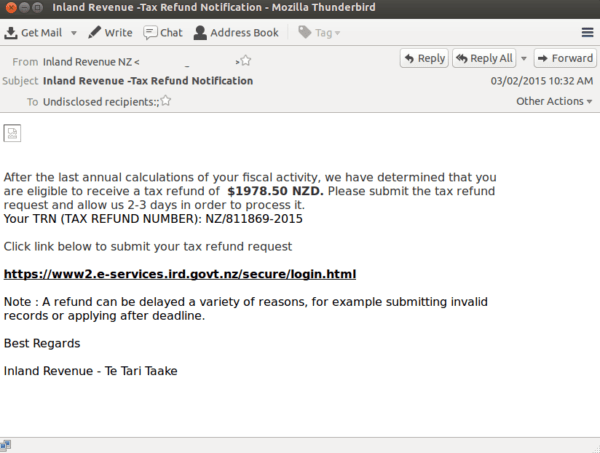
Millions of messages have been intercepted by Barracuda Real Time Systems and of the many, we notice the attacks happen both before and after a particular tax season anywhere around the world.
The phishing messages often take place well before the tax deadline and often target non-US citizens by requesting a W-8BEN form:
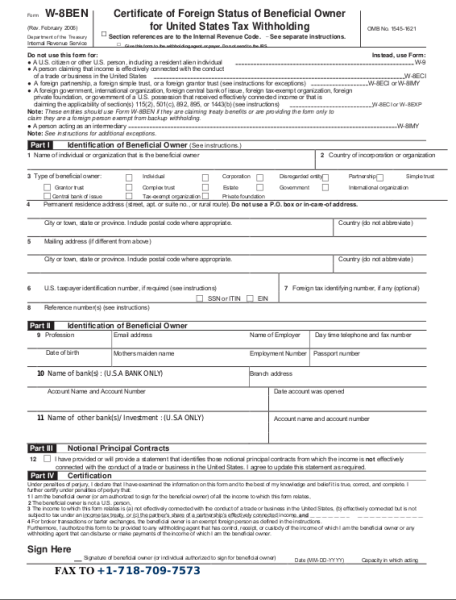
The growth of targeted attacks has reshaped the email security landscape with malware and spyware. Copy cats using ‘malware-for-pay’ similar to Zeus and other Trojan applications make it an inexpensive way for anyone to send malware and intercept all data.
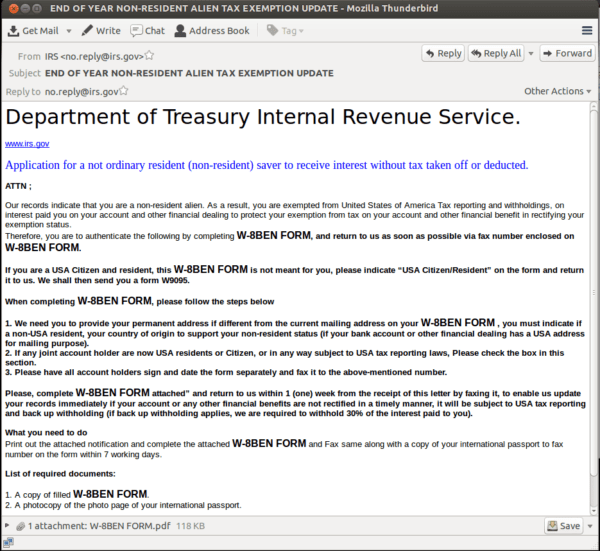
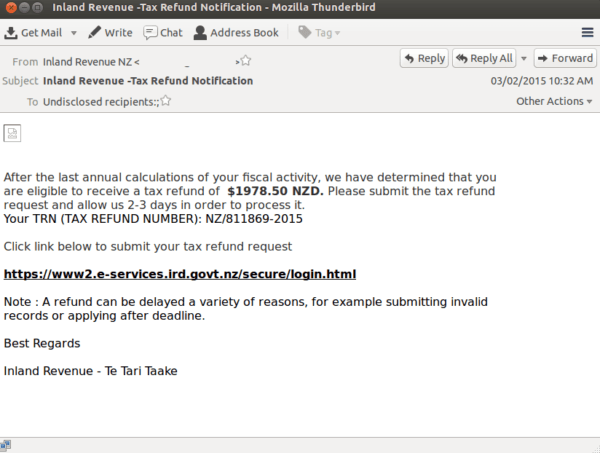
The goal for the attacker is to file returns before the victims, while adding bogus tax credits for a larger return. Taxpayers should, remain vigilant of the “After” tactics. In an effort to simply steal information for sale on the black market or for possible use the next year, the recipient is assumed to have already filed and is advised to once again either download malware or visit a fake tax agency website for more information.
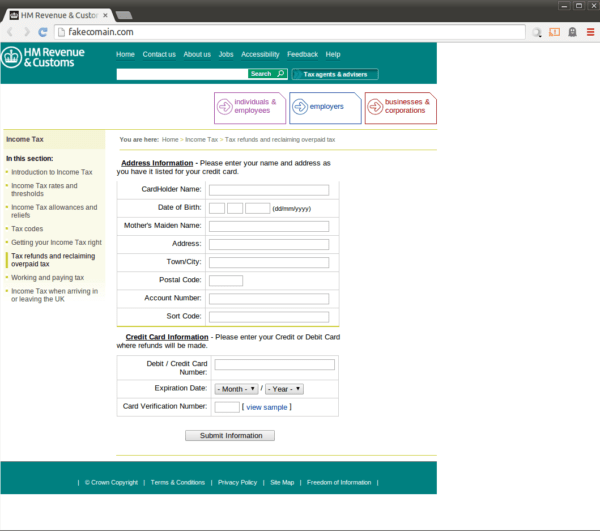
To avoid these type of scams, if you plan on using an online tax return website go to the site directly. Do not click on links that come through via email, especially if it comes from an anonymous sender. Do no not submit any sensitive information while using a public access hot spot. If possible (should always be an option) use a private or protected connection while filling out any type of forms that request sensitive information. Be proactive in your security approach.